Information Security News and Updates
Contact Us
The information security team is your point of contact for information, training, and resources to help you keep your personal and business data safe. Come here for information, tutorials, and news regarding cybersecurity.
Report an Incident
Have you experienced a security breach or do you suspect a threat? Submit a report here.
Contact Info
562-903-4740information.security@biola.edu
Featured Post

Upgraded Annual Cybersecurity Training!
May 17, 2024
Your annual cybersecurity awareness training is being upgraded this year!
This month we explain what to expect from Biola's new cybersecurity training platform.
Articles
Phishing Threats to Students
October 11, 2023
Attackers have been fraudulently impersonating university departments to trick students into paying them money.
This article guides Biola students on how to understand social engineering, recognize phishing attacks, and verify email credibility.
2023 National Cybersecurity Awareness Month at Biola
October 2, 2023
October is National Cybersecurity Awareness Month!
Here are some updates about a new cyber defense platform, what IT Information Security has done over the past year, and tips to improve your cybersecurity practices.
ChatGPT at Biola: Is AI Safe to Use?
May 15, 2023
AI tools have taken the world by storm — are they dangerous, or are they safe to use?
This article provides an overview of what ChatGPT is and how it should and should not be used for work.
Phone Security: Defense Against Smishing, Spear Phishing, and Spam
November 10, 2022
Biolans have been receiving malicious text messages on their personal cell phones claiming to be from Biola executives.
This month we explain how to defend yourself against SMS phishing, spear phishing, and spam on your phone.
Annual Update: Cybersecurity at Biola in 2022
October 5, 2022
October is National Cybersecurity Awareness Month.
So this month we provide our annual updates on the state of cybersecurity at Biola, and how you're involved.
Cybersecurity Compliance: Our Part and Yours
June 16, 2022
Cybersecurity can feel like red tape that gets in the way of your work. Why are there so many security requirements for employees?
This month we explain cybersecurity compliance requirements, and how you play a role.
Working Securely from Home
November 23, 2021
Phishing incidents increased by 220% last year, and are continuing to rise.
For this last week of National Cybersecurity Awareness Month, we provide a refresh on how you can protect yourself from phishing and social engineering.
Phishing RePhresh
October, 28 2021
Phishing incidents increased by 220% last year, and are continuing to rise.
For this last week of National Cybersecurity Awareness Month, we provide a refresh on how you can protect yourself from phishing and social engineering.
Back to Basics: 3 Quick Tips to Stay Secure
October, 15 2021
To observe NCSAM, we are reviewing three easy steps you can take today to become more security-minded and protect yourself from security threats.
The State of Cybersecurity at Biola in 2021
September 30, 2021
Every year for National Cybersecurity Awareness Month we take a moment to assess the past year. What have we been doing, and how has Biola improved?
Read this month's article to review our successes and get a sneak peak at what's coming in the next year.
You Can't Take It With You
March 5, 2021
This month we explain why and how you should keep your work and personal data separate in your employee Google account.
Be Smart, Restart
March 5, 2021
Did you know that attackers discover new vulnerabilities every day in operating systems and software, which they can exploit to steal your data?
This month we explain how simply restarting your computer regularly can protect you from these vulnerabilities.
Who Really Reads the Fine Print?
December 18, 2020
Every software purchase comes with risk because Biola's data is involved.
This month we explain IT’s technology review process, and how you can contribute to acquiring new software quickly and painlessly.
Google 2-Step Verification for Biola Faculty and Staff
November 28, 2020
In the near future, Google 2-Step Verification will be enforced for all Biola-managed email accounts.
This month, we explain what 2-Step Verification is and how to enable it.
Cybersecurity Month Episode 4: Suspicious Technology
October 26, 2020
For the final week of National Cybersecurity Awareness Month, Dave discovers the risk of using untrusted devices and programs.
Cybersecurity Month Episode 3: Computer Theft
October 19, 2020
For Week 3 of National Cybersecurity Awareness Month, Dave learns about physical device security when he leaves his computer unattended.
Cybersecurity Month Episode 2: Data Sharing
October 12, 2020
For Week 2 of National Cybersecurity Awareness Month, we review sound data sharing practices with another episode of this cybersecurity video series.
Cybersecurity Month Episode 1: Password Habits
October 6, 2020
For the first week of National Cybersecurity Awareness Month (NCSAM), we review secure password habits with the first episode of this humorous video series.
Where We Stand: Biola InfoSec in 2020
September 30, 2020
This month, we review our cybersecurity successes at Biola and prepare you for National Cybersecurity Awareness Month.
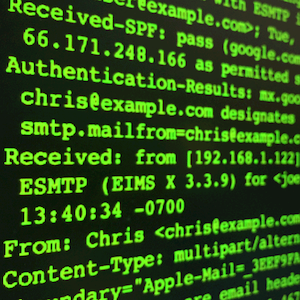
Spot Spoofing Like the Pros
August 25, 2020
Phishers use techniques that allow them to send email from another person's email address without logging in to their email account.
This month, we explain how you can use email headers to identify email address spoofing.
Can You Spot the Imposter?
July 23, 2020
Over the past few months, we have seen attackers continue to target Biola employees with imposter fraud in the form of phishing emails. Most often, these imposters use sender names as a disguise.
This month, we explain the importance of verifying a sender's email address.
Hackers Don't Break In, They Log In
June 22, 2020
These days, hackers don’t break in, they log in (with your credentials).
This month, we want to encourage you to keep your guard up. Phishing and social engineering attacks continue to be the most common attack vector used by cyber criminals.
Safeguarding Your Zoom Meetings
May 5, 2020
You may have heard Zoom’s name in the news recently, so we’d like to answer some of your security and privacy questions.
COVID-19 Scams to Watch Out For
April 22, 2020
Attackers are taking advantage of the COVID-19 situation to capitalize on the fear people experience during a crisis.
This month, we explain the most common COVID-19 scams we have seen since March, and ways you can stay safe.
Working Securely during the COVID-19 Pandemic
March 24, 2020
While working from home during the COVID-19 situation, it’s important to practice secure remote computing.
This month, we cover special considerations for working remotely, and for using a personally-owned computer for work.
Digital Inheritance: Your Data in Your Absence
February 20, 2020
Every day, as you interact with technology, you are adding to your digital presence at home and at work. When you’re no longer available, you’ll leave all your accounts and files behind as a digital inheritance for others to manage.
This month, we talk about safe ways to prepare your digital inheritance for others.
Prepare Your Data for Business Continuity
January 15, 2019
Have you ever been in a situation where you needed to access a coworker's business data, but they were out of the office or unavailable? These situations are common and illustrate the need for sound business continuity practices.
You are responsible to make business data available in your absence so that your team’s work can continue.
Where Should I Store Sensitive Data?
December 13, 2019
Sensitive data is any information that we don't make publicly available. But where should we store sensitive information? And how should we share it with our coworkers?
The way we store and share private information is the backbone of information security.
If You Collect It, Protect It
November 12, 2019
As an employee at Biola, if you collect any information about a person as part of your job, it’s your duty to secure that information, and use it responsibly.
This month, we look at data privacy..
Don't Be Manipulated by Social Engineering
October 24, 2019
For our last week of National Cybersecurity Awareness Month, we focus on your security-mindedness — specifically how to protect yourself against social engineering attacks.
Secure Your Tech with 7 Easy Tools
October 16, 2019
Own it. Secure it. Protect it. That’s the 2019 theme for National Cybersecurity Awareness Month.
This week, we review some simple but powerful tech tools for securing your devices and personal information.
Own Your Responsibility on Social Media
October 9, 2019
Social media is a great resource, but it doesn’t come without risks for you, your family, your friends, and your employer. When risk is present, we have a responsibility to keep ourselves and our community safe.
This week, we highlight three areas of responsibility when using social media sites.
Cybsersecurity at Biola - One Year Later
October 3, 2019
One year ago, during National Cybersecurity Awareness Month 2018, Biola launched our university’s Information Security Program.
So what have we being doing at Biola to stay secure?
Is My Smartphone Secure?
September 19, 2019
This month, we explain the many ways you can protect the information on your smartphone.
Don't Pay the Ransom
August 16, 2019
Ransomware is a type of malicious software that encrypts your files so that you can’t open them without a decryption key.
With a few simple habits, you can protect yourself and Biola against ransomware attacks.
Data Security Training at Biola
August 14, 2019
Biola requires all employees to complete mandatory data security training every year. IT assigns the training through the EverFi system.
Don't Forget to Back Up
July 23, 2019
Data is valuable. No one wants to lose the information stored on their computers.
The only way to protect yourself against data loss is through regular backups.
Safeguard Your WiFi Activity with VPN
June 17, 2019
Everyone likes free WiFi. But when you're doing Biola work from off campus, you need to make sure your network connection is protected from cyber attackers trying to steal your sensitive information.
You can use Biola’s VPN (Virtual Private Network) service to solve this problem..
Simulated Phishing at Biola
May 13, 2019
Simulated phishing is when an organization sends fake phishing emails to employees for the sake of training personnel to recognize phishing, and to gather response data.
At Biola, we use a simulated phishing tool called KnowBe4.
Protect Your Tech While Traveling
May 8, 2019
It’s the end of another year at Biola, and many of us have travel plans for the summer. So this month, we share tips for protecting your technology and personal information while traveling.
Keep What's Private, Private
April 15, 2019
We know that cyber attackers can target you using information they find on public websites.
But what about social network sites, where you choose what you reveal about yourself online? Your interests, location, habits, friends, and family. Attackers can use this information for nefarious purposes.
They Know Who You Are
March 15, 2019
Stay on guard.
Nearly every week, we see cyber attackers target specific Biola employees using personal information they find online. Learn how to best defend yourself against these targeted attacks.
Share Access, Not Passwords
February 14, 2019
We all know sharing passwords is unsafe. And yet, nearly every week, Biola employees log in to a
coworker’s computer or email account. This is a security risk.
This month, we give you solutions for sharing data access without sharing passwords.
Build the Unhackable Passphrase
January 15, 2019
Passphrases are more secure than traditional passwords against common hacking techniques, but are easier to create and to remember. Learn how you can create a passphrase that takes over 330 billion years to crack.
Stop Email Hackers with Google 2-Step
December 10, 2018
Turn on Google 2-Step Verification for your Biola email account right away. 2-Step is your best defense against phishing attacks. It takes about a minute to set up.
How to Avoid Getting Phished
November 9, 2018
Last year, nearly 500 Biolans were phished in a single day. You are a target for phishing attacks. Learn how to recognize phishing attacks, to make sure that you don't take the bait.
3 Easy Ways to Protect your Personal Information
October 15, 2018
In honor of National Cybersecurity Awareness Month, here are 3 easy things you can do right now to protect your personal information and stay safe online.
Equipping Biola Against Cyber Threats
October 1, 2018
Cyber attacks happen every day, and any one of us could be the point of a Biola data breach. In conjunction with National Cybersecurity Awareness Month, Biola's Information Security team is launching a new information security program for the university.
Protecting Your Account with 2-Factor Authentication
October 1, 2018
Learn how to use 2-factor authentication (2FA) to add an extra layer of security on top of your password. Use 2FA to keep other people out of your account, and set up the best defense against phishing attacks.